
Vulnerability Assessment and Penetration Testing (VAPT) is a critical practice for securing modern web applications. With cyber threats constantly evolving, organizations must proactively identify and fix security weaknesses before attackers exploit them. A structured VAPT process ensures thorough coverage, combining... Read more

Uniscan is a powerful tool that helps users discover potential vulnerabilities in their websites, providing them with actionable insights to strengthen their security.In this article, we will take a detailed look at Uniscan, how it works, and how you can... Read more

Introduction In the realm of cybersecurity, efficient tools are paramount for identifying vulnerabilities and securing systems. One such powerful tool is Gobuster, commonly used in Kali Linux environments. Gobuster excels at brute-forcing URIs, discovering hidden directories and files, finding DNS... Read more

In the ever-evolving landscape of cybersecurity, the need for robust tools that can help in auditing web applications is paramount. One such tool is DIRB, a powerful web content scanner designed to uncover existing and hidden web objects. This article... Read more
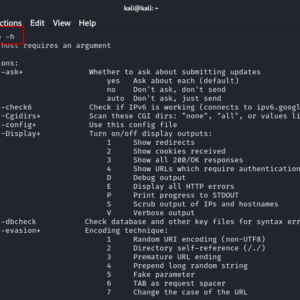
Web applications are increasingly vulnerable to various attacks, making security a top priority for developers and system administrators. Among the tools available for identifying these vulnerabilities, Nikto stands out as a robust web vulnerability scanner. Pre-installed in Kali Linux, Nikto... Read more

In the ever-evolving landscape of web security, HTTP Host header attacks have emerged as a significant threat. These attacks exploit vulnerabilities in how websites handle HTTP Host headers, leading to various security issues, including password reset poisoning. This article delves... Read more
