
Brute force attacks are one of the most basic yet effective ways of testing web application vulnerabilities. In this tutorial, we will demonstrate how to perform a brute force attack on a vulnerable web application using Burp Suite. Specifically, we... Read more

DirBuster is an essential tool for penetration testers and security professionals, allowing them to uncover hidden directories and files on web servers through brute force techniques. This multi-threaded Java application comes pre-installed in Kali Linux, a popular distribution used for... Read more
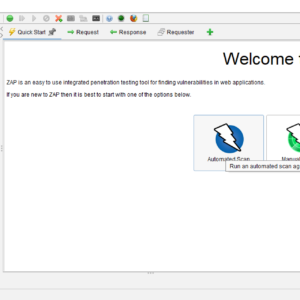
In the world of web application security, the OWASP Zed Attack Proxy (ZAP) stands out as one of the most versatile and user-friendly tools available. This open-source security scanner is an essential resource for both beginners and experienced professionals in... Read more

In the ever-evolving landscape of web security, HTTP Host header attacks have emerged as a significant threat. These attacks exploit vulnerabilities in how websites handle HTTP Host headers, leading to various security issues, including password reset poisoning. This article delves... Read more

Weevely is a stealth backdoor or PHP web shell that simulate telnet-like connection. This tool is used for post exploitation of vulnerability in web application. Syntax weevely generate <password> <file path> In this article we will do post exploitation of... Read more

