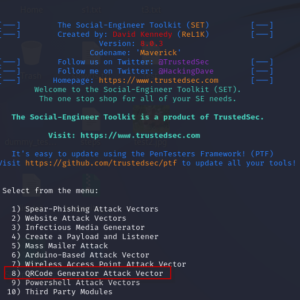
In the world of cybersecurity, social engineering is a powerful tool for exploiting human psychology to gain unauthorized access to systems and data. One of the most intriguing methods within the Social Engineering Toolkit (SET) is the QRCode Generator Attack... Read more

Website footprinting is a crucial phase in the information-gathering process of cybersecurity. It involves collecting as much data as possible about a target website to understand its structure, technologies in use, and potential vulnerabilities. This process is fundamental for attackers... Read more

Weevely is a stealth backdoor or PHP web shell that simulate telnet-like connection. This tool is used for post exploitation of vulnerability in web application. Syntax weevely generate <password> <file path> In this article we will do post exploitation of... Read more

NMAP, short for Network Mapper, is an essential and powerful network scanning tool available in Kali Linux. With its extensive range of features and flexibility, Nmap has become the go-to tool for network administrators, security professionals, and ethical hackers alike.... Read more
