
WPScan is a powerful, free, and open-source tool designed specifically for scanning WordPress websites for security vulnerabilities. It is one of the most widely used tools by ethical hackers and penetration testers to assess the security posture of WordPress installations.... Read more

Uniscan is a powerful tool that helps users discover potential vulnerabilities in their websites, providing them with actionable insights to strengthen their security.In this article, we will take a detailed look at Uniscan, how it works, and how you can... Read more

DirBuster is an essential tool for penetration testers and security professionals, allowing them to uncover hidden directories and files on web servers through brute force techniques. This multi-threaded Java application comes pre-installed in Kali Linux, a popular distribution used for... Read more
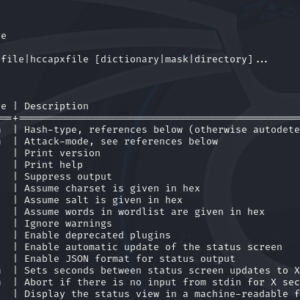
Hashcat is a powerful password recovery tool widely used for cracking hashes. It supports a variety of hash algorithms, including MD5, and can leverage wordlists to streamline the cracking process. This article will walk you through using Hashcat in Kali... Read more
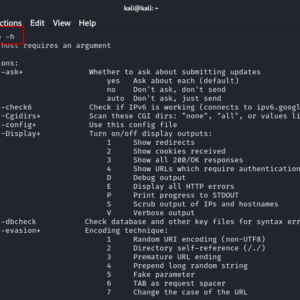
Web applications are increasingly vulnerable to various attacks, making security a top priority for developers and system administrators. Among the tools available for identifying these vulnerabilities, Nikto stands out as a robust web vulnerability scanner. Pre-installed in Kali Linux, Nikto... Read more

In today’s digital landscape, social engineering attacks have become increasingly prevalent. These attacks exploit human psychology rather than technical vulnerabilities to gain unauthorized access to sensitive information. One of the powerful tools used in these types of attacks is the... Read more

Weevely is a stealth backdoor or PHP web shell that simulate telnet-like connection. This tool is used for post exploitation of vulnerability in web application. Syntax weevely generate <password> <file path> In this article we will do post exploitation of... Read more

NMAP, short for Network Mapper, is an essential and powerful network scanning tool available in Kali Linux. With its extensive range of features and flexibility, Nmap has become the go-to tool for network administrators, security professionals, and ethical hackers alike.... Read more