
Web application security is more important than ever, with data breaches and cyberattacks becoming increasingly common. The OWASP Top 10 is a globally recognized list of the most critical security risks facing modern web applications. Published by the Open Web... Read more
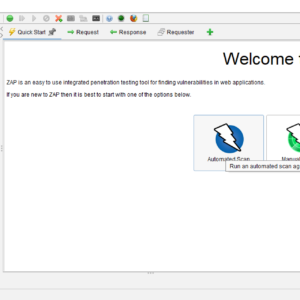
In the world of web application security, the OWASP Zed Attack Proxy (ZAP) stands out as one of the most versatile and user-friendly tools available. This open-source security scanner is an essential resource for both beginners and experienced professionals in... Read more

SQL Injection (SQLi) vulnerabilities represent one of the most significant threats to web applications today. By exploiting these vulnerabilities, attackers can gain unauthorized access to databases, allowing them to view, insert, delete, or modify records. This article will delve into... Read more