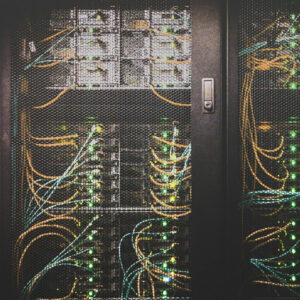
In today’s increasingly digital world, protecting networks from cyber threats is more critical than ever. Network security devices are essential tools that help prevent unauthorized access, data breaches, and cyberattacks. These devices act as barriers between the internal network and... Read more